Media Summary: You can buy me a coffee if you want to support the channel: I present In this video, we explain what "secret-sharing" is in a simple, approachable way. We also show how you can add up secret-shared ... Abroad Education Channel : Company Specific HR Mock ...
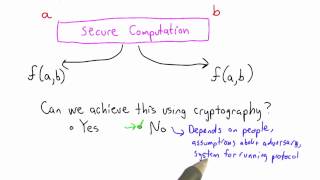
Secure Computation Applied Cryptography - Detailed Analysis & Overview
You can buy me a coffee if you want to support the channel: I present In this video, we explain what "secret-sharing" is in a simple, approachable way. We also show how you can add up secret-shared ... Abroad Education Channel : Company Specific HR Mock ... ... two main problems in adapting this to the