Media Summary: You can buy me a coffee if you want to support the channel: I present Paper by Melissa Chase, Yevgeniy Dodis, Yuval Ishai, Daniel Kraschewski, Tianren Liu, Rafail Ostrovsky, Vinod Vaikuntanathan ... Abroad Education Channel : Company Specific HR Mock ...
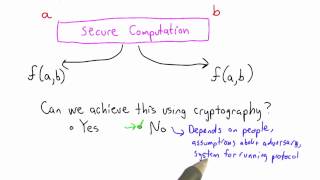
Secure Computation Solution Applied Cryptography - Detailed Analysis & Overview
You can buy me a coffee if you want to support the channel: I present Paper by Melissa Chase, Yevgeniy Dodis, Yuval Ishai, Daniel Kraschewski, Tianren Liu, Rafail Ostrovsky, Vinod Vaikuntanathan ... Abroad Education Channel : Company Specific HR Mock ... ... two main problems in adapting this to the RSA (Rivest–Shamir–Adleman) is an algorithm used to encrypt and decrypt messages. It is an asymmetric