Media Summary: Bitcoin and Cryptocurrency Technologies Online Course Lecture 2.5 - Want to learn more about AI and quantum tech? Visit our Academy Want to get in touch? Lecture 11: Smart card security model, Estonian ID card, Payment cards (EMV), Mobile phone SIM cards, Pay TV, attacks against ...
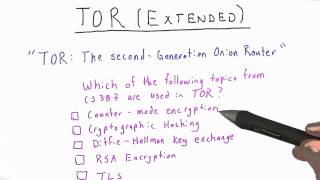
Putting It All Together Applied Cryptography - Detailed Analysis & Overview
Bitcoin and Cryptocurrency Technologies Online Course Lecture 2.5 - Want to learn more about AI and quantum tech? Visit our Academy Want to get in touch? Lecture 11: Smart card security model, Estonian ID card, Payment cards (EMV), Mobile phone SIM cards, Pay TV, attacks against ...