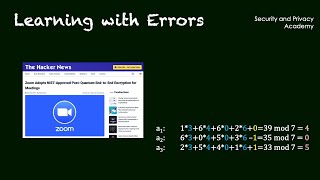
Media Summary: You can buy me a coffee if you want to support the channel: I This video is part of a module on lattice based cryptography. Let's construct a public-key cryptosystem based on the computational hardness of Module-LWE. This is unlikely to be vulnerable ...
Learning With Errors Explained - Detailed Analysis & Overview
You can buy me a coffee if you want to support the channel: I This video is part of a module on lattice based cryptography. Let's construct a public-key cryptosystem based on the computational hardness of Module-LWE. This is unlikely to be vulnerable ... ... (www.wire.com) ______ Post-Quantum Cryptography: Chris Peikert (University of Michigan, Ann Arbor) Lattices: Algorithms, Complexity, and Cryptography Boot Camp ... Video lectures for Alfred Menezes's introductory course on the mathematics of lattice-based cryptography. Kyber (ML-KEM) and ...
Authors: Alexander Poremba (California Institute of Technology) ITCS - Innovations in Theoretical Computer Science. The prospect of outsourcing an increasing amount of data storage and management to cloud services raises many new privacy ... Concepts such as Public Key Encryption, Trapdoor Permutations, the important LWE ( Talk at crypto 2013. Authors: Craig Gentry, Amit Sahai, Brent Waters. CIRM HYBRID EVENT Among the main candidates for post-quantum cryptography are systems based on the Ring In this video, we are going to discuss about
See this this is very hard problem that's why it was used in cryptography next is rlwe that is ring