Media Summary: Let's construct a public-key cryptosystem based on the computational hardness of See this this is very hard problem that's why it was used in cryptography next is rlwe that is ring MIT's Spring 2018 Cryptography & Cryptanalysis Class (6.875) Prof. Vinod Vaikuntanathan
Module Learning With Errors With Truncated Matrices - Detailed Analysis & Overview
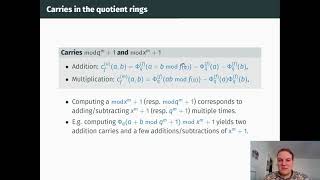
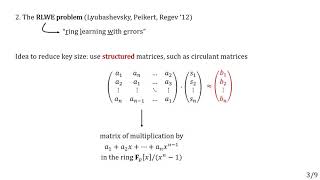
Let's construct a public-key cryptosystem based on the computational hardness of See this this is very hard problem that's why it was used in cryptography next is rlwe that is ring MIT's Spring 2018 Cryptography & Cryptanalysis Class (6.875) Prof. Vinod Vaikuntanathan Paper by Julien Devevey, Amin Sakzad, Damien Stehlé, Ron Steinfeld presented at PKC 2021 See ... Presentation filmed during the CIMPA School "SuSAAN – Summer School on Applied Arithmetic at Nesin" at Nesin Mathematics ... CIRM HYBRID EVENT Among the main candidates for post-quantum cryptography are systems based on the Ring
Chris Peikert (University of Michigan, Ann Arbor) Lattices: Algorithms, Complexity, and Cryptography Boot Camp ... Video lectures for Alfred Menezes's introductory course on the mathematics of lattice-based cryptography. Kyber (ML-KEM) and ... Talk at crypto 2013. Authors: Craig Gentry, Amit Sahai, Brent Waters. Lecture No.- 18 Matrix Method to Generate Error Correcting Codes The prospect of outsourcing an increasing amount of data storage and management to cloud services raises many new privacy ... Title: "On the security of the multivariate ring
Authors: Alexander Poremba (California Institute of Technology) ITCS - Innovations in Theoretical Computer Science. Talk at crypto 2013. Authors: Joël Alwen, Stephan Krenn, Krzysztof Pietrzak, Daniel Wichs. Here is the Python code: import sys import numpy as np import random public_key=[] vals ... Paper by Miruna Rosca and Amin Sakzad and Damien Stehlé and Ron Steinfeld, presented at Crypto 2017.