Media Summary: You can buy me a coffee if you want to support the channel: I explain The prospect of outsourcing an increasing amount of data storage and management to cloud services raises many new privacy ... CIRM HYBRID EVENT Among the main candidates for post-quantum cryptography are systems based on the
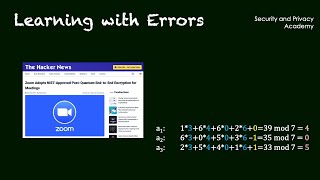
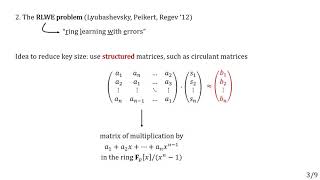
Ring Learning With Errors - Detailed Analysis & Overview
You can buy me a coffee if you want to support the channel: I explain The prospect of outsourcing an increasing amount of data storage and management to cloud services raises many new privacy ... CIRM HYBRID EVENT Among the main candidates for post-quantum cryptography are systems based on the Video lectures for Alfred Menezes's introductory course on the mathematics of lattice-based cryptography. Kyber (ML-KEM) and ... Title: Identity-Based Secure End-to-End Quantum-Safe MQTT Communication Using See this this is very hard problem that's why it was used in cryptography next is rlwe that is
Chris Peikert (University of Michigan, Ann Arbor) Lattices: Algorithms, Complexity, and Cryptography Boot Camp ... Title: "On the security of the multivariate Kristin Lauter's August 31 presentation at the 2015 UCI Mathematics of Cryptography Conference. Wouter Castryck and Ilia Iliashenko and Frederik Vercauteren, presented at Eurocrypt 2016. Paper by Maxime Bombar, Alain Couvreur, Thomas Debris-Alazard presented at Crypto 2022 See ... Paper by Rohit Chatterjee, Sanjam Garg, Mohammad Hajiabadi, Dakshita Khurana, Xiao Liang, Giulio Malavolta, Omkant Pandey ...
Paper by Tobias Oder and Tobias Schneider and Thomas Pöppelmann and Tim Güneysu, presented at CHES 2018. Presentation by Long Chen, Zhenfeng Zhang, Zhenfei Zhang at Crypto 2018 Rump Session. I will show reductions from and to the more well-established