Media Summary: Apple Reports Major Security Vulnerabilities on iPhones, iPads, and Macs Many SMBs have outdated firewalls, weak passwords, and poor segmentation, making them easy targets for attackers. It's crucial ... Stop Counterfeits: AI Protects Defense Supply Chains! Part
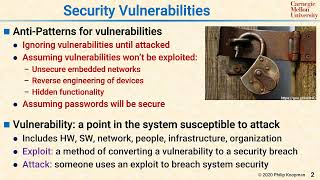
L39 01 Security Vulnerabilities Title - Detailed Analysis & Overview
Apple Reports Major Security Vulnerabilities on iPhones, iPads, and Macs Many SMBs have outdated firewalls, weak passwords, and poor segmentation, making them easy targets for attackers. It's crucial ... Stop Counterfeits: AI Protects Defense Supply Chains! Part Yuval Wollman, President of CyberProof, a UST company, shares why he's passionate about cybersecurity. ... Kevin Phillips, President & CEO of ManTech, explains why eliminating technical debt is critical to countering nation-state cyber ...