Media Summary: SaltStack SecOps 6.1 builds on the SaltStack automation of for continuous compliance and IT Where to view diagrams: Newsletter: Tools that ... A+ Training Course Index: Professor Messer's Course Notes: ...
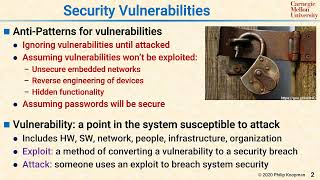
L39 02 Security Vulnerabilities Overview - Detailed Analysis & Overview
SaltStack SecOps 6.1 builds on the SaltStack automation of for continuous compliance and IT Where to view diagrams: Newsletter: Tools that ... A+ Training Course Index: Professor Messer's Course Notes: ... Welcome to our video lecture on "Mastering Wireless In this video, you'll learn how to reduce the attack surface of your environment by finding and fixing Are you preparing for the CompTIA Security+ or CC exam? Understanding the core concepts of threats, risks, and
In this video, I will be introducing you to the process of performing An AI's breakout revealed deep flaws in digital The landscape of local privilege escalation has fundamentally shifted with the public disclosure and active exploitation of ... In this video, I cover the following topics: Shared responsibility Client-based systems Server-based systems Integrated systems.