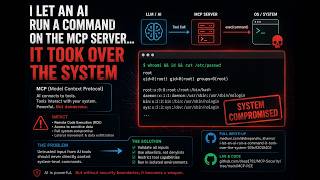
Media Summary: Imagine an API as a vending machine, you press a button, and you get what you want. But in Can an AI protocol be designed to execute ANY command an attacker sends? Yes, Anthropic's Model Context Protocol ( In this video, we dive into the world of AI
Mcp Security Vulnerabilities 101 - Detailed Analysis & Overview
Imagine an API as a vending machine, you press a button, and you get what you want. But in Can an AI protocol be designed to execute ANY command an attacker sends? Yes, Anthropic's Model Context Protocol ( In this video, we dive into the world of AI As AI agents move from simple chatbots to autonomous systems that execute tasks on our behalf, the DISCLOSURE: This video contains SGI (Synthetically Generated Information). Technical data is curated from recent 2026 ... As AI assistants connect deeper into real-world systems, the Model Context Protocol (
Learn from devastating real-world mistakes that led to massive financial losses, data breaches, and complete system ...


![[Session] MCP Security: The Exploit Playbook (And How to Stop Them) with Runlayer](https://i.ytimg.com/vi/guC1VeYZpQ4/mqdefault.jpg)