Media Summary: This playlist has a list of free videos from the course "Hacking and Securing Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter:
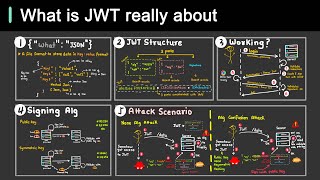
Jwt Web Security Vulnerabilities Attacks Best Practices Explained - Detailed Analysis & Overview
This playlist has a list of free videos from the course "Hacking and Securing Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Animation ... Get a Free System Design PDF with 158 pages by subscribing to our weekly newsletter: Support my work Here are a few tips on how to make your 1. Injection 2. Broken Authentication 3. Sensitive Data Exposure 4. XML External Entities 5. Broken Access Control 6. Learn the difference between session and token-based authentication on the web. Master
Become a senior software engineer with a job guarantee: Stay ahead of cybersecurity insights – Subscribe & turn on notifications! Let's learn about a neat trick you should know when ...