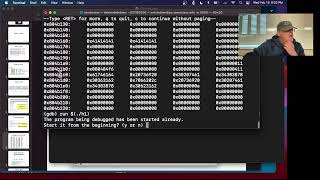
Media Summary: We are solving heap1 from exploit-exercises.com by exploiting a This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... A lecture for an Exploit Devlopment class More info:
Heap Overflow Gns3 - Detailed Analysis & Overview
We are solving heap1 from exploit-exercises.com by exploiting a This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... A lecture for an Exploit Devlopment class More info: Keep on learning with Brilliant at Get started for free, and hurry — the first 200 people get ... Want to prevent unauthorized devices from connecting to your network? In this video, you'll learn Port Security step-by-step using ... View the full free MOOC at This class is for C/C++ developers learning secure development, and ...
This paper presents Scatter, enabling the generation of exploitable heap layouts for