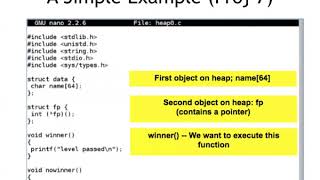
Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about We are solving heap1 from exploit-exercises.com by exploiting a
Buffer Overflow 5 Heap Overflow Demo - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about We are solving heap1 from exploit-exercises.com by exploiting a A college course in Exploit Development More info: This tutorial goes over the basic technique of how to exploit a Buffer Overflow Attack using Heap - Demo - part 2
Note on YouTube As I cannot include angled brackets in YouTube descriptions please ensure you place angled brackets around ... Binary and C source code are from pwnable.kr (bof level). ✘ My No-Nonsense C Programming Course: ... A college lecture at City College San Francisco. Based on "The Shellcoder's Handbook: Discovering and Exploiting Security ...