Media Summary: This is CS50 Explained, wherein David J. Malan and Doug Lloyd watch CS50's lectures and discuss the pedagogy behind CS50 ... Making yourself the all-powerful "Root" super-user on a computer using a Get QuizApp at: Welcome to our quiz app, the perfect ...
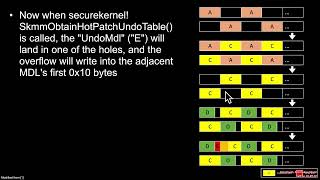
C Buffer Overflow Heap Stack Corruption And Analysis - Detailed Analysis & Overview
This is CS50 Explained, wherein David J. Malan and Doug Lloyd watch CS50's lectures and discuss the pedagogy behind CS50 ... Making yourself the all-powerful "Root" super-user on a computer using a Get QuizApp at: Welcome to our quiz app, the perfect ... Hello Everyone. In this video I am going to tell you about All right folks um today I want to show you in very simple terms how a View the full free MOOC at This class is for