Media Summary: 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ... Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
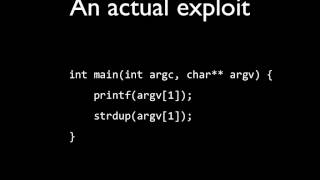
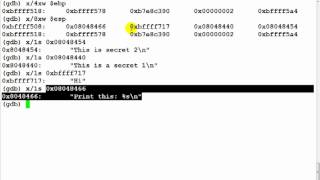
Format String Vulnerabilities Lunchbox - Detailed Analysis & Overview
7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ... Welcome to 'Information Security 5 Secure Systems Engineering' course ! This lecture introduces Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ Hi guys this is Alex and I'm going to give a brief introduction to using Hello hackers today we're going to be talking about Welcome to another exciting walkthrough from MetaCTF April 2024! In this video, I dive into the world of Binary Exploitation with a ...
Hi there! This video introduces the core ideas behind In this video, i'm introducing a new type of FORMAT STRING VULNERABILITIES 22VV1A1232 CNS ASSIGNMENT Format string vulnerabilities in ARM 2372626 Sven Morgenroth is the Security Researcher at Netsparker. Sven joins us again to talk about In this episode we combine the last two videos.