Media Summary: In this video, i'm introducing a new type of This video is for Educational purposes only. Want me to train you for Practical courses ... In this video I have discussed what format strings are, how they are used, and what are
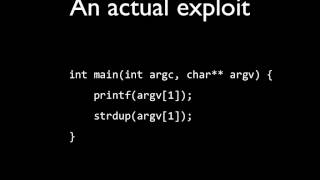
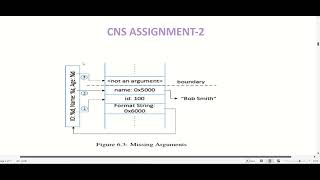
Lesson 5 Format String Attack - Detailed Analysis & Overview
In this video, i'm introducing a new type of This video is for Educational purposes only. Want me to train you for Practical courses ... In this video I have discussed what format strings are, how they are used, and what are Solving format1 from exploit-exercises.com with a simple Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ Hi there! This video introduces the core ideas behind
Hello hackers today we're going to be talking about format strings and If you would like to support me, please like, comment & subscribe, and check me out on Patreon: ... Hi guys this is Alex and I'm going to give a brief introduction to using In today's video, we explore the fascinating world of This video was created for an assignment for one of my classes. Hope it accurately describes this 7th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll look ...
UDEMY ADVANCED WHITE HAT HACKING AND PENETRATION TESTING Software Security on x86 and x64 architecture - how printf and











![Intro Format String Vulnerability | PicoCTF 2017 [39] "I've Got a Secret"](https://i.ytimg.com/vi/rkoP2mtwFNI/mqdefault.jpg)