Media Summary: Cryptography is scary. In this tutorial, we get hands-on with Node.js to learn how common crypto concepts work, like hashing, ... AWS Mumbai Summit 2018 Data protection is more important than ever. Maintaining confidentiality and integrity of your data at ... The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ...
Encryption For Everyone - Detailed Analysis & Overview
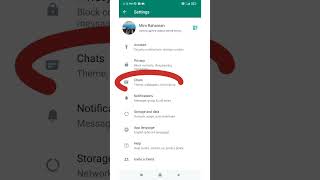
Cryptography is scary. In this tutorial, we get hands-on with Node.js to learn how common crypto concepts work, like hashing, ... AWS Mumbai Summit 2018 Data protection is more important than ever. Maintaining confidentiality and integrity of your data at ... The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... END-TO-END ENCRYPTION..saathi..security by Default. whatsapp security.. Join the free discord to chat: Join this channel to get access to perks: ... Session description: Due to recent events, e2ee has become a must have in any videoconferencing service, even if your service ...
Hak5 -- Cyber Security Education, Inspiration, News & Community since 2005: This time on the show - How to Mia Epner, who works on security for a US national intelligence agency, explains how cryptography allows for the secure transfer ... The stories that matter most to insiders, analysts, and business leaders. Delivered WhatsApp, iMessage, Android Messages and Signal How does public-key cryptography work? What is a private key and a public key? Why is asymmetric Jab Aap whatsapp ke tin dot par click karke linked device ke option par click karte hai to aapko link a device ke niche Your ...