Media Summary: Mia Epner, who works on security for a US national intelligence agency, explains how The debate between privacy and national security WhatsApp, iMessage, Android Messages and Signal
Everything You Need To Know About Encryption - Detailed Analysis & Overview
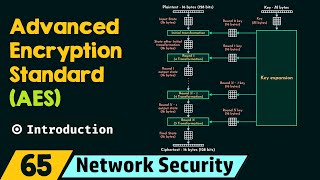
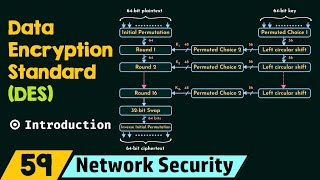
Mia Epner, who works on security for a US national intelligence agency, explains how The debate between privacy and national security WhatsApp, iMessage, Android Messages and Signal Presented by WWCode NYC From ciphers to cybersecurity, Network Security: Introduction to Advanced The most secure way to message someone privately is with a platform offering end-to-end
Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ...