Media Summary: Part 1 of 2 on heap exploitation, specifically about how the malloc() memory works and how it can be hacked. Part of Emory ... Part 2 of 2 of heap exploitation (demo). Format string exploits. Part of Emory University's This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ...
Cs453 Presentation One Byte Overflow - Detailed Analysis & Overview
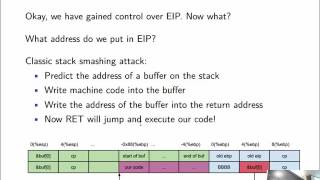
Part 1 of 2 on heap exploitation, specifically about how the malloc() memory works and how it can be hacked. Part of Emory ... Part 2 of 2 of heap exploitation (demo). Format string exploits. Part of Emory University's This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ... Making yourself the all-powerful "Root" super-user on a computer using a buffer This is CS50 Explained, wherein David J. Malan and Doug Lloyd watch CS50's lectures and discuss the pedagogy behind CS50 ... NOP sleds overcome address variability in buffer
This is CS50 Explained VR, wherein David J. Malan and Doug Lloyd (and you!) watch CS50's lectures and discuss the pedagogy ... Introduction to this class on computer security and hacking. Part of Emory University's integer vulnerabilities in C on x86 continued. Part of Emory University's