Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a MIT 6.858: Computer Systems Security Information about accessibility can be found at ... Keep on learning with Brilliant at Get started for free, and hurry — the first 200 people get ...
Cs453 Buffer Overflows - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a MIT 6.858: Computer Systems Security Information about accessibility can be found at ... Keep on learning with Brilliant at Get started for free, and hurry — the first 200 people get ... The first episode in a series covering x86 stack Hi everyone! I hope you enjoyed this video. Please do consider subscribing so we can continue making awesome hacking ... Part 1 of 2 on heap exploitation, specifically about how the malloc() memory works and how it can be hacked. Part of Emory ...
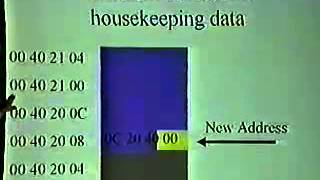
Part 2 of 2 of heap exploitation (demo). Format string exploits. Part of Emory University's CS513 2022 Lecture 6 Memory Vulnerabilities Buffer Overflow Problems This video is part of an online course, Software Debugging. Check out the course here: