Media Summary: Master CSDF Unit 5 – Computer Forensic Analysis & Validation in just ONE Shot! This video covers the entire chapter with ... Want to Become Highly Paid Hacker & Investigator ? Attend FREE Online Hacking Workshop ... This video introduces external write blockers used to prevent changes to suspect disks during
Computer Forensics Validation Forensic Data - Detailed Analysis & Overview
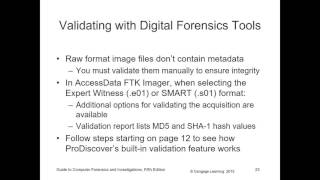
Master CSDF Unit 5 – Computer Forensic Analysis & Validation in just ONE Shot! This video covers the entire chapter with ... Want to Become Highly Paid Hacker & Investigator ? Attend FREE Online Hacking Workshop ... This video introduces external write blockers used to prevent changes to suspect disks during validating forensic data and addressing data hiding techniques in computer forensics Can you trust your digital evidence? In this in-depth lecture from Chapter 9 of the Guide to Media files are more than pictures, audio, or video — they are layered containers of evidence. In this lecture, we break down how ...
In this video you will learn how to use Autopsy to investigate a local hard drive. - CompTIA Security+ (SY0-701) - Objective 4.8: ... Find all lecture notes, past papers, Assignments, text books and many other documents on gpa elevator @ Forensics analysis and validation in computer forensics This presentation is as part of Anna University Sponsored FDTP on CS8074 - Cyber