Media Summary: Can you trust your digital evidence? In this in-depth lecture from Find all lecture notes, past papers, Assignments, text books and many other documents on gpa elevator @ How do you know your digital evidence is authentic? In this episode of our
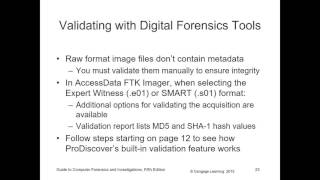
Module 9 Digital Forensics Analysis Validation Chapter 9 Tools Hashing Data Integrity - Detailed Analysis & Overview
Can you trust your digital evidence? In this in-depth lecture from Find all lecture notes, past papers, Assignments, text books and many other documents on gpa elevator @ How do you know your digital evidence is authentic? In this episode of our 0:11 Lab 9.1 Using Autopsy to Search for Keywords in an Image 28:42 Lab 9.2 In this video you will understand all about what is by: PSSg Art Gargarita Biñas Anti Cybercrime Unit.