Media Summary: How do you know your digital evidence is authentic? In this episode of our Find all lecture notes, past papers, Assignments, text books and many other documents on gpa elevator @ Thanks to advanced technologies, hackers have become adept at infiltrating networks. However, even cybercriminals leave traces ...
Digital Forensics Analysis Validation Computer Forensics Investigation Course - Detailed Analysis & Overview
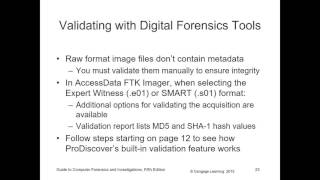
How do you know your digital evidence is authentic? In this episode of our Find all lecture notes, past papers, Assignments, text books and many other documents on gpa elevator @ Thanks to advanced technologies, hackers have become adept at infiltrating networks. However, even cybercriminals leave traces ... Forensics analysis and validation in computer forensics