Media Summary: You're literally one click away from a better setup — grab it now! As an Amazon Associate I earn ... Abroad Education Channel : Company Specific HR Mock ... More exclusive content: Twitter: Blog: ...
Code Review Vulnerability Of Encryption Class Using Aes Hmac - Detailed Analysis & Overview
You're literally one click away from a better setup — grab it now! As an Amazon Associate I earn ... Abroad Education Channel : Company Specific HR Mock ... More exclusive content: Twitter: Blog: ... TIMESTAMPS ⏰ ▭▭▭▭▭▭ 00:07:35 Vickie starts her presentation ▭▭▭▭▭▭ ABSTRACT & BIO ▭▭▭▭▭▭ Writing ... In this video we explore the concepts of MACs. We first explore why Hashing alone is not enough, which leads us into the ... Hook Security isn't an afterthought — it's a requirement. From securing user passwords
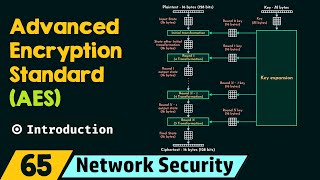
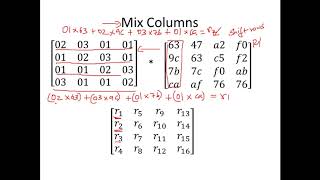
This is one of the many videos in the mini-series of HTTPS ... Network Security: Introduction to Advanced The purpose of this video is to introduce users to basic In this lecture we will be learning 1. The steps inside each round in