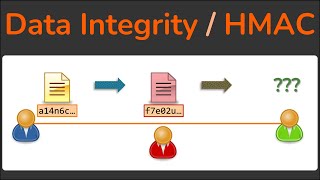
Media Summary: More exclusive content: Twitter: Blog: ... This is one of the many videos in the mini-series of HTTPS ... In this video we explore the concepts of MACs. We first explore why
Hmac Explained Keyed Hash Message Authentication Code - Detailed Analysis & Overview
More exclusive content: Twitter: Blog: ... This is one of the many videos in the mini-series of HTTPS ... In this video we explore the concepts of MACs. We first explore why Abroad Education Channel : Company Specific HR Mock ... Hi Friends, SUPER THANKS is enabled by YouTube and if any viewer want to contribute any financial support (not mandatory) ... Bit flipping a stream cipher could help you hit the Jackpot! But not with
... and the most common implementation of a MAC known as the This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... Three types of Authentications 1. Message Encryption 2. Interested in studying cybersecurity at the highest level? Bochum offers one of the most advanced academic environments for ... There's an updated video at or search for 105 This video is part of an online course, Web Development. Check out the course here:
Prove the integrity of a message over an untrusted network with the