Media Summary: You're literally one click away from a better setup — grab it now! As an Amazon Associate I earn ... More exclusive content: Twitter: Blog: ... Abroad Education Channel : Company Specific HR Mock ...
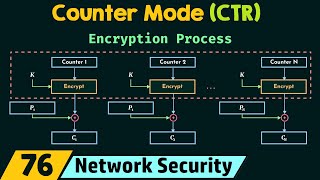
Code Review Aes Ctr Mode Encryption With Hmac - Detailed Analysis & Overview
You're literally one click away from a better setup — grab it now! As an Amazon Associate I earn ... More exclusive content: Twitter: Blog: ... Abroad Education Channel : Company Specific HR Mock ... Bit flipping a stream cipher could help you hit the Jackpot! But not with This is one of the many videos in the mini-series of HTTPS ... In this video we explore the concepts of MACs. We first explore why Hashing alone is not enough, which leads us into the ...
Paper by Jin Hyung Park, Dong Hoon Lee, presented at CHES 2018. See Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... Interested in studying cybersecurity at the highest level? Bochum offers one of the most advanced academic environments for ... This video is part of an online course, Applied You don't just 'run a cipher' - you need a In this video, we break down Message Authentication