Media Summary: In this video we discuss how to find where EIP is overwritten using Binary Reduction (aka Binary Search) External Links: Dino Dai ... Ultimate Ethical Hacking Full Course For Beginners [ In this demo I walk through the process of using a
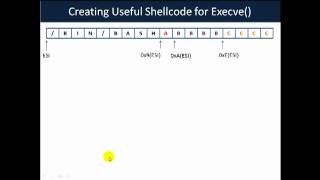
Buffer Overflow Tutorial Part 5 - Detailed Analysis & Overview
In this video we discuss how to find where EIP is overwritten using Binary Reduction (aka Binary Search) External Links: Dino Dai ... Ultimate Ethical Hacking Full Course For Beginners [ In this demo I walk through the process of using a Making yourself the all-powerful "Root" super-user on a computer using a Join us for Kubernetes Forums Seoul, Sydney, Bengaluru and Delhi - learn more at kubecon.io Don't miss KubeCon + ... SQL Injections - 5 Buffer Overflow Exploit
Buffer-Overflow Attack demonstrated by SRIVATSAN V


![Buffer Overflow Attack || Ultimate Ethical Hacking Full Course For Beginners [ Part - 5 ] 🚀🔥👨💻🛜](https://i.ytimg.com/vi/lTquBUGrXNQ/mqdefault.jpg)












