Media Summary: Making yourself the all-powerful "Root" super-user on a computer using a Buffer-Overflow Attack demonstrated by SRIVATSAN V Windows Custom Shell coding (Buffer Overflow) - Mihir
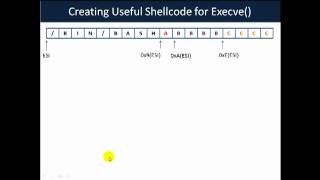
Buffer Overflow Part 5 Popping The Shell - Detailed Analysis & Overview
Making yourself the all-powerful "Root" super-user on a computer using a Buffer-Overflow Attack demonstrated by SRIVATSAN V Windows Custom Shell coding (Buffer Overflow) - Mihir This tutorial goes over the basic technique of how to In the final video of the series we generate our In this demo I walk through the process of using a
In this video we will take a look at finding a suitable instruction address, such as JMP ESP, that we can place inside of EIP. Join us for Kubernetes Forums Seoul, Sydney, Bengaluru and Delhi - learn more at kubecon.io Don't miss KubeCon + ...









![[ 7 ] - Buffer Overflow - Generating shell code in MSF & Popping a shell](https://i.ytimg.com/vi/q6f-uvIIXq0/mqdefault.jpg)

![[ 5 ] - Buffer Overflow - Locating JMP ESP Instruction](https://i.ytimg.com/vi/-KEN0I-G3qk/mqdefault.jpg)




