Media Summary: Video a scopo educativo, non mi assumo nessuna responsabilità se provocate danni a terzi o altro. Vediamo come exploitare una ... Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about
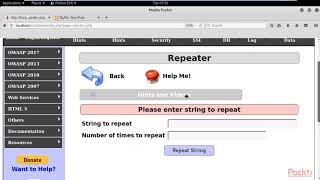
Buffer Overflow Attack M I T S - Detailed Analysis & Overview
Video a scopo educativo, non mi assumo nessuna responsabilità se provocate danni a terzi o altro. Vediamo come exploitare una ... Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about This tutorial goes over the basic technique of how to buffer overflow buffer overflow attack in cyber security, cyber security tutorial cs 503 what is buffer overflow attack ... Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
Security+ Training Course Index: Professor Messer's Course Notes: ... ... used for current runtime operations now a This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ... We updated this video for accuracy and improved graphics. Please view the new version here:
![Buffer Overflow Attack [M.i.t.S.]](https://i.ytimg.com/vi/cokLu8JekSQ/mqdefault.jpg)