Media Summary: MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: James ... Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about
3 Buffer Overflow Exploits And Defenses - Detailed Analysis & Overview
MIT 6.858 Computer Systems Security, Fall 2014 View the complete course: Instructor: James ... Making yourself the all-powerful "Root" super-user on a computer using a Hello Everyone. In this video I am going to tell you about Worried about hackers overflowing your computer's Buffer Overflow - 13 Defense Against Buffer Overflows We updated this video for accuracy and improved graphics. Please view the new version here:
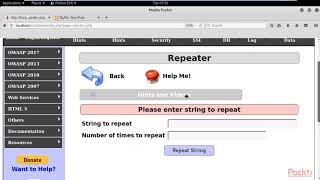
This video tutorial has been taken from Web Security. You can learn more and buy the full video course here ... Hi everyone! I hope you enjoyed this video. Please do consider subscribing so we can continue making awesome hacking ... This tutorial goes over the basic technique of how to All right hello and welcome to a quick stream on our video on MIT 6.858: Computer Systems Security Information about accessibility can be found at ... This lecture is part of my undergraduate security course at the University of Cambridge. 00:00 Challenges and intro 01:40 What is ...
Wanna learn to hack? Join my new CTF platform: In this video we explore the dangers of