Media Summary: Welcome to 'Information Security 5 Secure Making yourself the all-powerful "Root" super-user on a computer using a Buffer Overflow - 14 Programming Countermeasures
Operating System 38 How To Prevent Buffer Overflow Attacks - Detailed Analysis & Overview
Welcome to 'Information Security 5 Secure Making yourself the all-powerful "Root" super-user on a computer using a Buffer Overflow - 14 Programming Countermeasures This is a series of three videos, which gives a quick start up on different exploitation and mitigation techniques for the Security+ Training Course Index: Professor Messer's Course Notes: ... The PEN-200 course material is copyright Offensive Security. Video presented by John C. Kirk. Georgia Weidman's article: ...
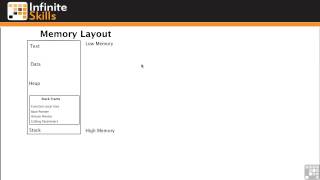
Team Hotel -- IFT 381-- Arizona State University. 1203 Protecting Against Buffer Overflow Attacks In this video, we will be learning How to perform Speaker: Martin Johns An overview of static and dynamic approaches A talk that will present academic tools, which are designed ... Buffer Overflow - 13 Defense Against Buffer Overflows