Media Summary: CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... In this session, we break down one of the most critical topics in Welcome back to AlphaVerse. In this video, we are learning about
Access Control Models Explained Dac Mac Rbac Cybersecurity For Beginners - Detailed Analysis & Overview
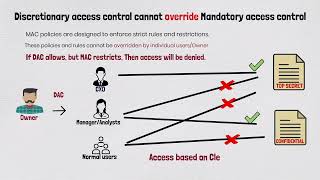
CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... In this session, we break down one of the most critical topics in Welcome back to AlphaVerse. In this video, we are learning about How do organizations decide who can access what data or systems? It all comes down to Get the threat intelligence guide → Learn about the technology → Exploring the ... In this video, we dive into Domain 3 of the ISC2 Certified in
Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... Welcome to TechBit Academy! TechBit Academy is your go-to place for learning computer technologies, core computer ... In this video, we will understand Non-Discretionary Hello and welcome to this third video in our lecture on In this lecture we will discuss about : What is













![[Computer Security] Access control policies [3/9]: Discretionary access control (DAC) and AC matrix](https://i.ytimg.com/vi/mN9qX1Qm10s/mqdefault.jpg)


