Media Summary: CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... In this session, we break down one of the most critical topics in cybersecurity — Get the threat intelligence guide → Learn about the technology → Exploring the ...
Access Control Models Explained Dac Mac Rbac Abac - Detailed Analysis & Overview
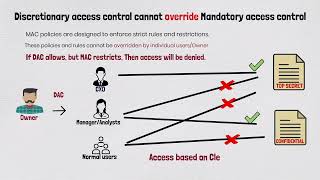
CyberPlatter Discord Channel: Website: Security Analyst and Engineer ... In this session, we break down one of the most critical topics in cybersecurity — Get the threat intelligence guide → Learn about the technology → Exploring the ... How do organizations decide who can access what data or systems? It all comes down to Role-based access control (RBAC) is an essential method for managing permissions in cloud systems. In this video, Varun sir ... Welcome back to AlphaVerse. In this video, we are learning about
Welcome to Gumzo Cyber Security Podcast. Confused about GATE Insights Version: CSE or GATE Insights Version: CSE ... In this video, we dive into Domain 3 of the ISC2 Certified in Cybersecurity exam, focusing on CISSP (Certified Information Systems Security Professional) Domain-5 and CCSP (Certified Cloud Security Professional) ... Welcome to Lesson 26 of the 100 Days of Cybersecurity Challenge. In this lesson, we break down If you've ever worked with software that needs to keep things secure and organized, you've probably heard of