Media Summary: There are a lot of tutorials on ROP out there, so I try to explain the concept in a different way. Maybe that's a bad idea and a lot ... Hi guys my name is Alex and I'm going to give a brief introduction to In this series, we learn to work with pwntools and ROP gadgets. Video 1: Environment Setup Resources: ...
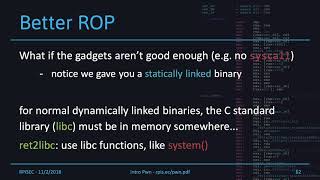
390r 6 Return Oriented Programming - Detailed Analysis & Overview
There are a lot of tutorials on ROP out there, so I try to explain the concept in a different way. Maybe that's a bad idea and a lot ... Hi guys my name is Alex and I'm going to give a brief introduction to In this series, we learn to work with pwntools and ROP gadgets. Video 1: Environment Setup Resources: ... All right so today we're talking about an introduction to ... attacks in particular you will focus on Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔
Our engineering director Huck talk about BROP, a binary exploitation tactic that can be used when you don't have access to the ... In this video, we will take a look at using In previous weeks, we've gone over techniques like shellcoding to inject our own malicious code into an executable, but many of ...