Media Summary: In this video, we will take a look at using MOST VIDEOS ARE UNDER THE LIVE SECTION! In this video I walk through an example of ROP tutorial step by step, explained in detail. We will understand how
Return Oriented Shellcode - Detailed Analysis & Overview
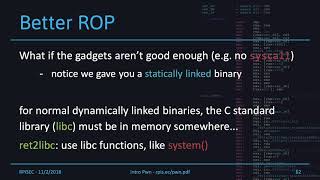
In this video, we will take a look at using MOST VIDEOS ARE UNDER THE LIVE SECTION! In this video I walk through an example of ROP tutorial step by step, explained in detail. We will understand how 5th video from the "Practical Buffer Overflow Exploitation" course covering the basics of Binary Exploitation. In this video we'll see ... We write our first real exploit to get root access. Solving stack5 from exploit-exercises.com with a simple Buffer Overflow and ... by Giorgos Poulios & Christoforos Ntantogian & Christos Xenakis The downside of current polymorphism techniques lies to the ...
A college lecture at City College San Francisco. Based on "The Shellcoder's Handbook: Discovering and Exploiting Security ... Let's learn some historical context behind ROP! Module information at pwn.college/modules/rop. Hi guys my name is Alex and I'm going to give a brief introduction to Let's learn about combining memory corruption with There are a lot of tutorials on ROP out there, so I try to explain the concept in a different way. Maybe that's a bad idea and a lot ... I often get questions about not working exploits. Sometimes the problem is the
Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ In previous weeks, we've gone over techniques like