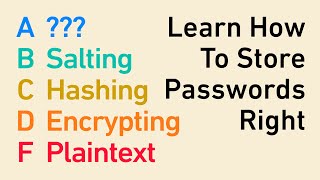
Media Summary: Hashing vs Encryption Deep Difference Explained (With Real Examples) Confused between Hashing and Encryption? 🤔 You’re not ... Welcome to AV cyber active channel where we discuss cyber Security related topics. Feel free to Comment if you want more ... Hello everyone in this tutorial we will learn
Why Your Data Isnt Safe Hashing Vs Encryption Explained - Detailed Analysis & Overview
Hashing vs Encryption Deep Difference Explained (With Real Examples) Confused between Hashing and Encryption? 🤔 You’re not ... Welcome to AV cyber active channel where we discuss cyber Security related topics. Feel free to Comment if you want more ... Hello everyone in this tutorial we will learn SOC Interview Questions and Answers. These have been