Media Summary: 01:50 What is Hashing? 03:27 What is Encryption? 05:32 Encoding vs Go to to subscribe to the full list of courses and get source code for projects. How is IITK - Advanced Executive Program in Cybersecurity ...
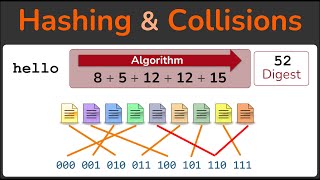
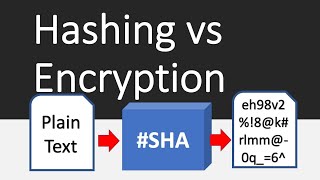
Hashing Vs Encryption - Detailed Analysis & Overview
01:50 What is Hashing? 03:27 What is Encryption? 05:32 Encoding vs Go to to subscribe to the full list of courses and get source code for projects. How is IITK - Advanced Executive Program in Cybersecurity ... Welcome to AV cyber active channel where we discuss cyber Security related topics. Feel free to Comment if you want more ... Thanks for watching! I hope this video helped you understand how it all works. If you found it useful, hit the like button, subscribe ... Hashing vs Encryption Deep Difference Explained (With Real Examples) Confused between Hashing and Encryption? 🤔 You’re not ...
Three types of Authentications 1. Message







![[Hindi] What is Hashing with Example | Hashing Algorithm | MD5 | SHA256](https://i.ytimg.com/vi/tzB5VD-DzJE/mqdefault.jpg)