Media Summary: In Lab05, we learned that even when DEP and ASLR are applied, there are application-specific contexts that can lead to full ... Let's learn some historical context behind Hi guys my name is Alex and I'm going to give a brief introduction to
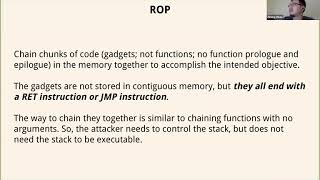
Tut06 1 Return Oriented Programming Rop - Detailed Analysis & Overview
In Lab05, we learned that even when DEP and ASLR are applied, there are application-specific contexts that can lead to full ... Let's learn some historical context behind Hi guys my name is Alex and I'm going to give a brief introduction to This video will demonstrate how to perform an automatic Help the channel grow with a Like, Comment, & Subscribe! ❤️ Support ➡ ↔ ... slot for return address is already taken by argument
Okay so um today we are going to talk about uh This research provides innovative contributions to