Media Summary: At the Black Hat USA 2025 conference in Las Vegas, we announced the discovery of 9 zero-day Share part of a secret without knowing which part? Dr Tim Muller explains how Oblivious Transfer works. This webinar took place on Wednesday 24 June 2020. Since the first networks were implemented more than 20 years ago, ...
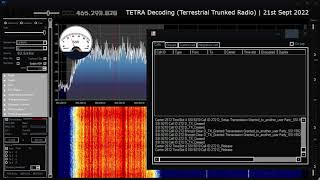
Tetra Vulnerability Tetra Burst Computerphile - Detailed Analysis & Overview
At the Black Hat USA 2025 conference in Las Vegas, we announced the discovery of 9 zero-day Share part of a secret without knowing which part? Dr Tim Muller explains how Oblivious Transfer works. This webinar took place on Wednesday 24 June 2020. Since the first networks were implemented more than 20 years ago, ... In this talk we will discuss the radio jailbreaking journey that enabled us to perform the first public disclosure and analysis of the ... Midnight Blue, a specialist security consulting firm, announced today the discovery of 5 zero-day An oldie but a goodie, Dr Mike Pound revisits the Log-Jam attack. Original Log Jam paper: Thanks to ...
In this talk we will discuss the radio jailbreaking journey that ... Extracting a secret key by simply watching the flickering of an LED? Sounds implausible but that's what we're discussing with Dr ... How do we measure harm to improve the performance of Ai in the real world? Dr Hana Chockler is a Reader in Computer Science ...