Media Summary: this video contains a visual explanation of IITK - Advanced Executive Program in Cybersecurity ... WhatsApp, iMessage, Android Messages and Signal all use the super-secure system called
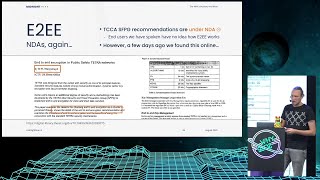
Tetra Air Interface And E2e Encryption - Detailed Analysis & Overview
this video contains a visual explanation of IITK - Advanced Executive Program in Cybersecurity ... WhatsApp, iMessage, Android Messages and Signal all use the super-secure system called The debate between privacy and national security has never been more heated, with Apple and other tech firms going up against ... In this video, I'll walk you through setting up your very own self-hosted, private messaging app using Matrix—a decentralized, ... END-TO-END ENCRYPTION..saathi..security by Default. whatsapp security..
System Design for SDE-2 and above: System Design for Beginners: ...