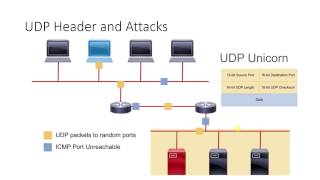
Media Summary: Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... The UDP is a connectionless transport-layer protocol that provides an interface between IP and upper-layer processes. by Gabi Nakibly In this work we present a massively large-scale survey of Internet traffic that studies the practice of false content ...
Tcp Vulnerabilities And Attacks 4 - Detailed Analysis & Overview
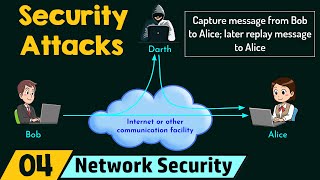
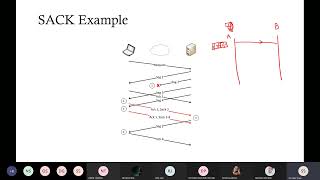
Gate Smashers Shorts: Watch quick concepts & short videos here: Subscribe ... The UDP is a connectionless transport-layer protocol that provides an interface between IP and upper-layer processes. by Gabi Nakibly In this work we present a massively large-scale survey of Internet traffic that studies the practice of false content ... In this video I talk about the importance of randomizing the initial sequence number. It used to possible to establish a In this video, we break down the inherent JFrog in collaboration with Forescout Research Labs recently released the fourth study from Project Memoria - the industry's most ...
1Describing Common TCP IP Attacks CCNP SOC Network Security - A better way to prepare for Coding Interviews LinkedIn: ...