Media Summary: In the past few years, there's been a rise in critical JFrog in collaboration with Forescout Research Labs recently released the fourth study from Project Memoria - the industry's most ... Welcome to our latest video about ethical hacking! In this video, we'll explore the basics of ethical hacking, including what it is, ...
05 Tcp Stack Vulnerabilities - Detailed Analysis & Overview
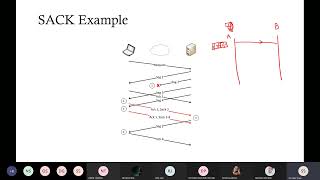
In the past few years, there's been a rise in critical JFrog in collaboration with Forescout Research Labs recently released the fourth study from Project Memoria - the industry's most ... Welcome to our latest video about ethical hacking! In this video, we'll explore the basics of ethical hacking, including what it is, ... In this video, we break down the inherent This stream starts off with 20-30 minutes of talk around Hping transforms your command line into a packet artillery cannon, firing custom
This is an educational course on the topic of Network Security and Penetration Testing. We will try to understand what is Network ... CS642 - Computer Security - Spring 2019 Network ⚠️ Disclaimer: This video is strictly for educational purposes only. All demonstrations are conducted in a controlled ... Join us as we delve into the intricacies of