Media Summary: Project for compsci, 90/90! video and image usage under fair use law, using 7 seconds or less of the videos. Images and other ... Security+ Training Course Index: Professor Messer's Course Notes: ... Hello Everyone. In this video I am going to tell you about
Software Security Vulnerabilities Integer Buffer Overflow - Detailed Analysis & Overview
Project for compsci, 90/90! video and image usage under fair use law, using 7 seconds or less of the videos. Images and other ... Security+ Training Course Index: Professor Messer's Course Notes: ... Hello Everyone. In this video I am going to tell you about Making yourself the all-powerful "Root" super-user on a computer using a We updated this video for accuracy and improved graphics. Please view the new version here: Team 6 (Jonathan Ojeda / Santiago Cabrieles)
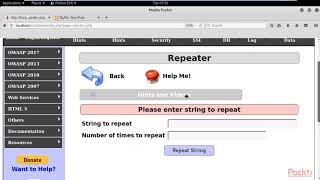
This video tutorial has been taken from Web In this video walk-through, we covered a scenario of