Media Summary: In this lecture we will be taking a detailed look at all the steps in Requirements of hash Function Simple Hash Function Link for playlists: Link for our website: ...
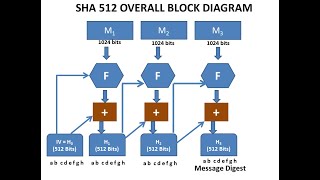
Sha 512 Algorithm - Detailed Analysis & Overview
In this lecture we will be taking a detailed look at all the steps in Requirements of hash Function Simple Hash Function Link for playlists: Link for our website: ... Abroad Education Channel : Company Specific HR Mock ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... This is the ultimate guide to the Secure Hash Algorithm (SHA), specifically mastering the SHA-512 standard. We start by ...
Hello students now we are going to discuss about Thanks for watching my video...!☺️☺️☺️☺️☺️☺️ Hello guys ♀️ This is Pooja...! I'll try to explain the concept of ... In recent years, the most widely used hash function has been the secure hash In this video, we explain the SHA-512 Hash Algorithm, which is one of the most secure cryptographic hash functions used in ... In this video, we dive into the fascinating world of hashing and how it transforms data. You'll learn how hashing You might have heard of hash functions. You might have heard of