Media Summary: In this lecture we will be taking a detailed look at all the steps in Abroad Education Channel : Company Specific HR Mock ... Link for playlists: Link for our website: ...
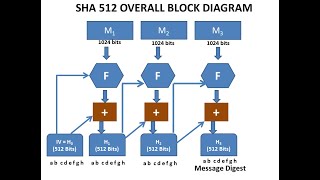
Secure Hash Algorithm Sha 512 - Detailed Analysis & Overview
In this lecture we will be taking a detailed look at all the steps in Abroad Education Channel : Company Specific HR Mock ... Link for playlists: Link for our website: ... Myself Shridhar Mankar a Engineer l YouTuber l Educational Blogger l Educator l Podcaster. My Aim- To Make Engineering ... This is the ultimate guide to the Secure Hash Algorithm (SHA), specifically mastering the SHA-512 standard. We start by ... Distribution of secret keys-mod 5: Distribution of Public keys-Mod 5:
Hello students now we are going to discuss about In recent years, the most widely used hash function has been the IITK - Professional Certificate Program in Blockchain (India Only) ...