Media Summary: In this episode we show you how to hide your ass and browse safe and anonymously with the help of a web You're literally one click away from a better Securing SSH servers by restricting only key based authentication. Disallowing password based authentication mechanism to ...
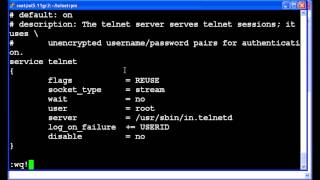
Redirecting Telnet Telnet Proxy Configuration Networknuts - Detailed Analysis & Overview
In this episode we show you how to hide your ass and browse safe and anonymously with the help of a web You're literally one click away from a better Securing SSH servers by restricting only key based authentication. Disallowing password based authentication mechanism to ... Other units in this course below: Unit 1: Unit ...