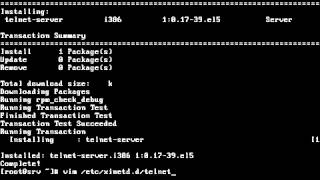
Media Summary: How To Configure Telnet Proxy Chains Server How To Install How to Configure Telnet Server in Red Hat Enterprise Linux - 5 Telnet Server Configuration in RedHat Enterprise Linux 5 www wtuto com YouTube
How To Configure Telnet Proxy Chains Server Redhat 5 - Detailed Analysis & Overview
How To Configure Telnet Proxy Chains Server How To Install How to Configure Telnet Server in Red Hat Enterprise Linux - 5 Telnet Server Configuration in RedHat Enterprise Linux 5 www wtuto com YouTube Telnet Server Configuration in RedHat Enterprise Linux 5 www wtuto com YouTube2 Anonymity is one of the most important elements for the penetration tester (hacker). Imagine if a pentester or a black hat hacker ...