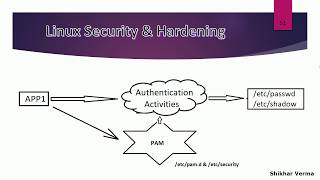
Media Summary: This video explains about how we can block suspicious When a user opens a text console and logs in Hi everyone, a few days ago I came across a LinkedIn post about pamspy, I decided to search more about the functionality.
Red Hat Linux Tutorial 71 Pluggable Authentication Modules Pam - Detailed Analysis & Overview
This video explains about how we can block suspicious When a user opens a text console and logs in Hi everyone, a few days ago I came across a LinkedIn post about pamspy, I decided to search more about the functionality. You're literally one click away from a better setup — grab it now! As an Amazon Associate I earn ... A real world example of when you might use links. When you dont want authconfig to overwrite your password-auth or other ...