Media Summary: Join us as we delve into the intricate world of IDM (Identity Management) is the RHEL-based version of the FreeIPA project. It gives you centralized control over users, groups, ... When a user opens a text console and logs in
Red Hat Linux Pam Authentication 2 And Firewall Redhatlinux Linuxtutorial Linuxtutorial - Detailed Analysis & Overview
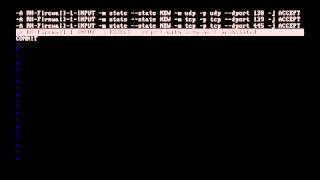
Join us as we delve into the intricate world of IDM (Identity Management) is the RHEL-based version of the FreeIPA project. It gives you centralized control over users, groups, ... When a user opens a text console and logs in Sometimes people leave your organization and you need to disable or delete their account. But you also have other types of ...