Media Summary: ... to run estrace estrace is a command that'll shows us the CIS calls that are executed inside of the TIMESTAMPS ⏰ ▭▭▭▭▭▭ 00:07:35 Vickie starts her presentation ▭▭▭▭▭▭ ABSTRACT & BIO ▭▭▭▭▭▭ Writing ... This video is part of the Udacity course "Intro to Information
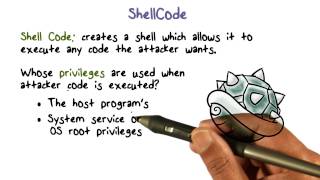
Program Security Shellcoding Tips - Detailed Analysis & Overview
... to run estrace estrace is a command that'll shows us the CIS calls that are executed inside of the TIMESTAMPS ⏰ ▭▭▭▭▭▭ 00:07:35 Vickie starts her presentation ▭▭▭▭▭▭ ABSTRACT & BIO ▭▭▭▭▭▭ Writing ... This video is part of the Udacity course "Intro to Information SANS PenTest HackFest 2022 Speaker: Jean-François Maes, Certified Instructor, SANS Institute In this presentation, ... In this talk we'll look at a process for beginning to analyze Windows syscalls for many years had virtually never been used due to the portability problem associated with syscall system ...
The SecurityTube Linux Assembly Expert (SLAE) is an online course and certification which focuses on teaching the basics of ... Frequently in malware investigations, we come across Description: In the dynamic realm of cybersecurity, understanding exploit development is paramount. Delve into the intricate world ... Welcome to "Enhancing Cybersecurity: Mastering Welcome to part 8! In this video, I'll introduce a small utility I developed for testing and debugging I often get questions about not working exploits. Sometimes the problem is the
This is the second video continuing through the freely available Corelan Tutorials! More specifically, in this video we will be ...






![[SecurityTube.net] Shellcoding Basics](https://i.ytimg.com/vi/T7GtWid5hsw/mqdefault.jpg)









