Media Summary: This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... This playlist has a list of free videos from the course "Exploit Development for Linux (x86)". If you are interested in viewing the full ... Welcome to part 03. In this video, we'll cover how to use x32dbg to debug
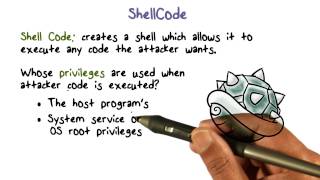
Shellcode Privileges - Detailed Analysis & Overview
This video is part of the Udacity course "Intro to Information Security". Watch the full course at ... This playlist has a list of free videos from the course "Exploit Development for Linux (x86)". If you are interested in viewing the full ... Welcome to part 03. In this video, we'll cover how to use x32dbg to debug Join us in-person and virtually at our Wild West Hackin' Fest: information security conferences — Let's learn about subtleties in the writing of kernel A Visual Studio extension that provides a simple yet powerful interface for encrypting
Be better than yesterday In this video, we will look into the typical techniques and methods on how to execute In this second installment of the 'Become a Malware Analyst Series," Principal Incident Response & Research Consultant Scott ... Let's learn about combining memory corruption with This is binary exploitation tutorial. Get a remote shell by